And It Proves the Mullahs Are Still Coming for Us Even While Getting Bombed Into the Stone Age
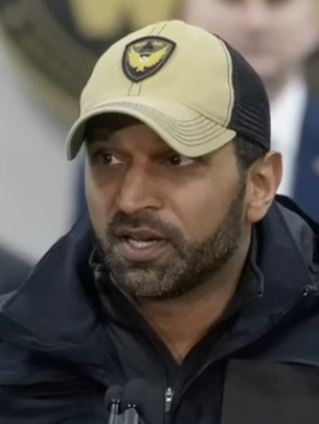
The mullahs in Tehran just scored a cheap propaganda win by hacking FBI Director Kash Patel’s old personal Gmail account and dumping personal photos and emails online. No classified material got out. Nothing from official systems. Just old selfies, travel receipts, family shots, and a resume from years before he took the top job at the Bureau. The hackers – a pro-Iran crew tied straight to Tehran’s intelligence machine – called it retaliation and posted the haul on March 27, 2026. Patel’s team and the Bureau moved fast, locked things down, and confirmed the breach was real but harmless to national security. That’s the official line. Here’s the America First reality: this hack shows exactly why personal security for top officials matters and why the Iranian regime remains a direct threat even as American and Israeli strikes keep pounding their nuclear dreams into dust.
The Hack That Shouldn’t Have Happened But Did
The breach hit an old personal account Patel used before becoming Director. Emails stretched back to around 2010 through 2019 – the kind of stuff regular Americans have sitting in their inboxes: hotel bookings, business notes, mirror selfies, family pictures. The hackers, operating under the name Handala Hack Team, posted more than 300 items and bragged about it on their site. They claimed they cracked the “impenetrable” systems in hours. The Bureau pushed back hard: no government networks touched, no secrets compromised, just historical personal data from before Patel ran the show.
BREAKING 🚨
🇺🇸 📧 A U.S. official confirms FBI Director Kash Patel’s personal email account was hacked.
🇮🇷 The Iranian state-backed “Handala Hack Team” claims responsibility.
📷 They’ve reportedly posted Patel’s resume and several old photos online. pic.twitter.com/fSuXrpy1Iv
— FalconUpdatesHQ (@FalconUpdatesHQ) March 27, 2026
The timing was no accident. This came days after the FBI seized domains linked to the same crew and while the U.S. is still hammering Iranian targets in the ongoing war. Tehran’s hackers framed it as payback for Patel vowing to hunt them down and for the reward the State Department slapped on the group – up to ten million dollars for information leading to their identification. Classic Iranian playbook: when you can’t win on the battlefield, you try to embarrass your enemies with stolen vacation photos.
What the Counter-Investigation Actually Turned Up
The FBI didn’t sit idle. They went right back after the hackers the moment the breach surfaced. What they confirmed is straightforward and damning: this wasn’t some basement-dwelling script kiddie. The operation came from a group U.S. officials have long tied to Iran’s Ministry of Intelligence and Security. These are state-backed actors running “hack and leak” ops designed to harass, humiliate, and sow doubt. They hit Patel because he’s the face of the crackdown on Iranian cyber threats and because personal accounts are softer targets than hardened government systems.
The discovery drives home a hard truth about the Middle East mess. Iran’s regime is reeling from American and Israeli strikes that gutted its nuclear program and command structure, yet it still has the reach to target a top U.S. official’s private email. That reach relies on proxies, cutouts, and the kind of asymmetric warfare Tehran has perfected – cheap hacks, propaganda dumps, and enough plausible deniability to keep the diplomats talking. No grand conspiracy with American lobbyists emerged from the probe. What did emerge is confirmation that Iranian intelligence is still playing the long game, using cyber as a weapon while their conventional forces crumble. They want to make the cost of confronting them feel personal.
Why This Matters More Than the Mullahs’ Latest Tantrum
This hack exposes a weakness every American should understand. Top officials live in the same digital world the rest of us do. Personal emails get used for everything from booking flights to chatting with family. When those accounts get hit, the enemy gets pictures, travel patterns, and contacts that can be weaponized for influence or future targeting. The fact that it was an old account doesn’t make it less embarrassing. It makes it a warning: if they can get to the FBI Director’s Gmail, they can get to anyone who isn’t careful.
The regime in Tehran is desperate. Their nuclear sites are smoking craters. Their proxies are on the run. Their economy is in freefall. So they pull stunts like this – steal some selfies, post them online, and pretend they’ve struck a blow. It’s pathetic. But it also proves they haven’t been deterred. They’re still probing, still testing, still trying to divide us and make us look weak.
What Happens Next – And What America First Demands
The Bureau and the administration are already moving. Mitigation steps are in place. The ten-million-dollar reward stays live. Investigations into the hackers continue with every tool available. Expect more domain seizures, more sanctions on anyone who helps these crews, and tighter rules on personal device security for senior officials. No more treating private accounts like they’re off-limits to state actors.
For the rest of us, the lesson is simple and brutal. Lock down your own digital life the way the professionals now have to. Strong passwords, two-factor everything, no reusing old accounts for sensitive stuff. The enemy doesn’t care if you’re the FBI Director or a regular working stiff – they want leverage anywhere they can find it.
This hack changes nothing on the battlefield. Iran is still losing the real war. American strikes keep hitting hard, and the mullahs keep bleeding. But it does remind every patriot why America First means staying vigilant at home while we finish the job overseas. The regime that sends hackers after personal emails is the same regime that mined the Strait of Hormuz and funded terror for decades. They don’t get to dictate terms through embarrassment.
Patel and the team are handling it like professionals. The rest of the country should take the hint: secure what’s yours, support the fight against the real threats, and keep the pressure on until the last Iranian threat is neutralized. The selfies don’t matter. The resolve does. And America still has plenty of that.